Defense suppliers don’t have the luxury of “getting to CMMC when we get to it” anymore. 2026 is not a stable year. Threats are louder, supply chains are messier, and the DoD is done waiting for the industrial base to catch up.
Here’s the blunt reality: waiting 18 months for CMMC certification is a strategy for losing contracts. Not “maybe.” Not “in some cases.” It’s simply the wrong move when your eligibility to bid, and your ability to keep work already awarded, depends on proving you can protect Controlled Unclassified Information (CUI) now.
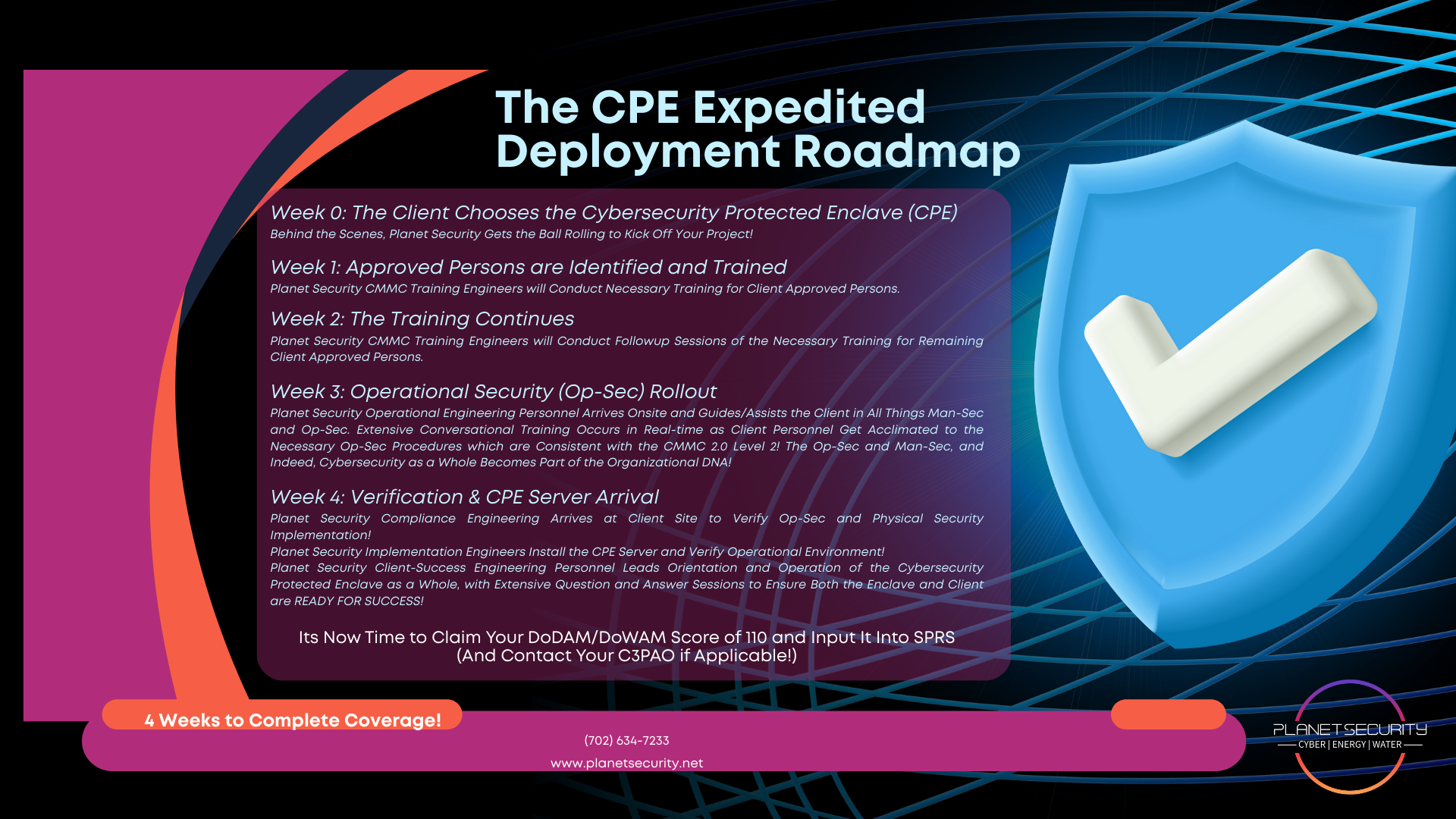
This is exactly why CPE Level 2 plus Yoo-Jin AI exists: CMMC 2.0 Level 2 readiness in 4 weeks, with the hard parts enforced automatically, 900+ hardening steps and 1,500+ checkpoints handled continuously.
The Phase 2 reality: the clock is already running
CMMC rollout timing is not theoretical anymore.
- Phase 1 runs through November 9, 2026
- Phase 2 begins November 10, 2026
- Starting Phase 2, CMMC 2.0 Level 2 third-party certification becomes mandatory for prioritized CUI contracts
- C3PAO backlogs are already forming (and they will get worse, not better)
Even if your environment is clean today, the certification pipeline is not. When everyone rushes the same narrow door at the same time, your timeline becomes somebody else’s calendar.
And the assessment itself? In the real world, it often takes 6–12 months once you account for remediation, evidence, documentation cleanup, scheduling, and rework.
So if you’re starting in 2026 and you’re still thinking “we’ll be ready in a year,” you’re already behind.
Why “18 months” is a dangerous fantasy (and not just a compliance problem)
I’ll say the quiet part out loud: CMMC is not only a security standard, it’s a contract survival standard.
If your organization touches CUI and you can’t prove protection at the required level, you risk:
- Being ineligible to bid on new work
- Getting cut out of subcontractor roles (prime contractors won’t carry your risk)
- Contract delays while your customer waits for compliance confirmation
- Contract termination if you can’t meet compliance clauses or data handling obligations
- A reputation hit that’s hard to recover from in the defense ecosystem
This is why speed is the only strategy for 2026: the cost of delay isn’t “extra effort.” It’s lost revenue and lost trust.
CMMC 2.0 Level 2 isn’t “a few controls”, it’s the whole system
To be clear, CMMC 2.0 Level 2 maps to NIST SP 800-171 Rev. 2 and requires:
- 110 CMMC requirements
- 320 assessment objectives
- A real, defensible environment: policies, procedures, technical enforcement, evidence, and operational discipline
And you don’t get to hand-wave it with “we’re working on it.” The real world looks like this:
- You need an SSP that matches reality
- You need evidence that’s current, consistent, and repeatable
- You need the environment to stay compliant after you “finish”
Most organizations that “take 18 months” aren’t slow because they want to be. They’re slow because they’re trying to build a compliant enclave from scratch across mixed systems, mixed admins, and mixed habits.
That’s exactly the trap CPE Level 2 avoids.
The 4-week alternative: CPE Level 2 + Yoo-Jin AI

CPE Level 2 is not “consulting.” It’s not a stack of tools with a checklist. It’s an engineered, hardened, operational environment designed for one thing:
Unbreakable security + continuous CMMC 2.0 Level 2 technical compliance, fast.
And Yoo-Jin AI is the force multiplier: it helps drive consistency, monitoring, and validation without exposing your sensitive data to generic AI platforms.
What “4 weeks” actually means
In four weeks, you’re not “starting your journey.” You’re building a working, governed enclave where:
- Controls aren’t “planned”, they’re implemented
- Evidence isn’t “hunted”, it’s produced
- Security isn’t “aspirational”, it’s enforced
This isn’t magic. It’s automation + architecture + hardening discipline.
900+ hardening steps and 1,500+ checkpoints, handled automatically
Let’s talk about what usually crushes teams: the sheer volume of technical work, repeated validation, and never-ending drift.
With CPE Level 2, you’re not manually chasing every hardening action across endpoints, servers, identity, logging, and configuration baselines.
You get:
- 900+ hardening steps applied as part of the enclave build
- 1,500+ checkpoints continuously validated (so compliance doesn’t decay the moment someone clicks the wrong setting)
That matters because CMMC success is not about “passing once.” It’s about being able to prove, at any point, that your environment is operating as claimed.
Automation is the difference between “audit panic” and “audit confidence.”
“Unbreakable” security: what that really means for defense suppliers

When we say unbreakable security, we’re not talking about buzzwords. We’re talking about a posture that assumes:
- You will be targeted
- You will be probed
- Your users will make mistakes
- Attackers will use credential theft, lateral movement, and persistence tactics
- Nation-state capability is in play (directly or indirectly)
So the system is designed to limit blast radius, enforce least privilege, harden defaults, and produce verifiable operational evidence.
The contract impact (this is the part people underestimate)
Unbreakable security is not just “nice security.” It’s how you:
- Keep CUI from leaking
- Keep your prime contractor from dropping you
- Keep the DoD confident you’re not the weak link
- Keep revenue from getting shut off due to compliance failure
If you’re a supplier, you’re not just protecting your own business. You’re protecting your place in a supply chain that’s actively being targeted.
Why generic AI tools can’t be trusted with CUI (and what we do differently)
Let’s be crystal clear: generic AI tools are not safe for client data in a defense compliance context.
If your staff is pasting snippets into public AI chat tools, even “just for help writing a policy” or “summarizing a ticket”, you’ve introduced a new, hard-to-track data handling risk. And if any of that includes sensitive contract details, drawings, export-controlled info, or operational context, the risk is bigger than most teams realize.
That’s why Planet Security emphasizes AI-obfuscated data when using AI-enabled workflows. In plain English:
- You get the benefits of AI assistance and operational acceleration
- Without feeding raw client secrets into Big-Tech AI systems
- And without creating an AI-shaped hole in your compliance story
Yoo-Jin AI supports speed, but not at the cost of confidentiality.
If you want the technical overview of Yoo-Jin, see: https://planetsecurity.net/yoo-jin
What you actually get with CPE Level 2 (practical, not fluffy)
Here’s what most defense suppliers want, stated plainly:
- “Give me a compliant environment.”
- “Make it fast.”
- “Make it defensible to auditors.”
- “Don’t bury my team in ongoing maintenance.”
- “Don’t blow up my operations.”
CPE Level 2 is built to deliver exactly that, by design.
CPE Level 2 is engineered for:
- CMMC 2.0 Level 2 alignment across the full scope (110 requirements and 320 objectives)
- Continuous technical compliance monitoring
- Operational survivability during major cyber events
- Documentable, repeatable evidence (the thing audits live or die on)
- Reduced compliance workload (less human chasing, more automated enforcement)
And because the enclave is purpose-built, you’re not spending months arguing about tool sprawl, log gaps, identity mismatches, and policy-vs-reality contradictions.
Pricing (because you need to plan, not guess)
Pricing should never be the headline, but you still need real numbers to make decisions.
A common starting point for CPE Level 2 is:
- $1,299/month for up to 20 users
- Includes the secure enclave environment, continuous technical compliance and security monitoring, and the automated hardening/compliance enforcement approach that drives rapid readiness
And yes, deployment choices affect cost:
- Choose an 8-week deployment instead of 4 weeks and pricing drops by $100/month (because the resourcing intensity is spread out)
Again: don’t obsess over the monthly number. Obsess over the real business outcome:
Staying eligible. Staying defensible. Staying paid.
Q&A: the questions defense suppliers are asking right now
Q: “Can we wait until late 2026 and still be fine?”
Not safely. Phase 2 starts November 10, 2026, and C3PAO scheduling backlogs are already forming. If your plan depends on “we’ll find an assessor when we’re ready,” your plan is depending on luck.
Q: “We’re small: does this urgency apply to us too?”
Yes. In supply chains, smaller subs often get hit hardest because primes will cut risk quickly. If you touch CUI, you’re in the compliance blast radius.
Q: “What’s the biggest reason companies fail CMMC readiness efforts?”
Two big ones:
- They try to retrofit compliance onto messy environments instead of using a controlled enclave model.
- They underestimate evidence and consistency. Controls must be real, operating, and provable: not “we plan to.”
Q: “Why is CPE Level 2 faster than traditional approaches?”
Because it’s not “assemble tools and hope.” It’s a pre-engineered, hardened, monitored environment with 900+ hardening steps and 1,500+ checkpoints baked in and continuously validated.
Q: “Does using AI create compliance risk?”
Using generic AI tools absolutely can. That’s why Planet Security differentiates with AI-obfuscated data in Yoo-Jin AI workflows: so you can move fast without leaking sensitive content into third-party models.
The bottom line: speed protects contracts
If you remember one thing from this post, make it this:
Speed isn’t about convenience. Speed is about continuity.
Continuity of eligibility. Continuity of trust. Continuity of revenue.
In 2026’s threat environment: and with Phase 2 deadlines and assessor backlogs tightening: waiting 18 months is how suppliers get cut off.
If you want the fastest path to a hardened, defensible, always-on compliant environment, start here: CPE Level 2