The defense contracting world is full of bad advice. Everywhere you turn, someone's selling the dream of "just add more software to your existing network" and magically achieve CMMC compliance. It's the biggest myth in cybersecurity today, and it's costing defense suppliers time, money, and their sanity.
Let's cut through the noise and talk about why the all-in-one approach is a recipe for disaster: and how CPE Level 2 offers a real solution that actually works.
The "All-in-One" Myth: Why It's Everywhere
Here's the pitch you've probably heard: "Why buy new hardware when you can just layer our software on top of what you already have?" It sounds reasonable. It sounds cost-effective. It sounds like exactly what a busy defense supplier wants to hear.
The problem? It's complete nonsense.
The all-in-one myth persists because it tells people what they want to hear. Nobody wants to rip out their existing infrastructure. Nobody wants to learn new systems. Everyone wants the magic button that makes CMMC compliance happen overnight without changing anything.

But here's what actually happens when you try to force CMMC compliance onto your existing business network:
- Configuration nightmares that take months to sort out
- Security gaps that auditors will find immediately
- Performance issues that slow down your entire operation
- Audit failures that cost you contracts and credibility
Why the All-in-One Approach Always Fails
Let's get specific about why trying to retrofit CMMC compliance onto your existing network is like trying to turn your family minivan into a Formula 1 race car by slapping racing stripes on it.
Complex Configurations Create Vulnerabilities
Your existing network wasn't designed for CMMC. It was designed to run your business efficiently, not to protect Controlled Unclassified Information (CUI) according to NIST SP 800-171 standards.
When you start layering compliance software on top of business systems, you create a patchwork of configurations that nobody fully understands. Each new piece of software interacts with existing systems in unexpected ways. The result? A complex web of potential failure points that grows more tangled every day.
Higher Chance of Audit Failure
CMMC auditors aren't impressed by good intentions. They want to see clean, documented, repeatable security controls that actually work. When your compliance approach involves dozens of different software packages trying to work together, proving that everything functions correctly becomes nearly impossible.
The documentation alone becomes a nightmare. How do you document the interaction between 15 different security tools when half of them weren't designed to work together in the first place?
Security Gaps Are Inevitable
Here's the dirty secret about the all-in-one approach: it creates more security problems than it solves. When you're trying to force business systems and compliance systems to coexist on the same network, something always gets compromised.
Maybe it's the firewall rules that get loosened to accommodate business applications. Maybe it's the monitoring that gets disabled because it interferes with daily operations. Every compromise creates a gap that attackers can exploit.

Enter CPE Level 2: The Real Solution
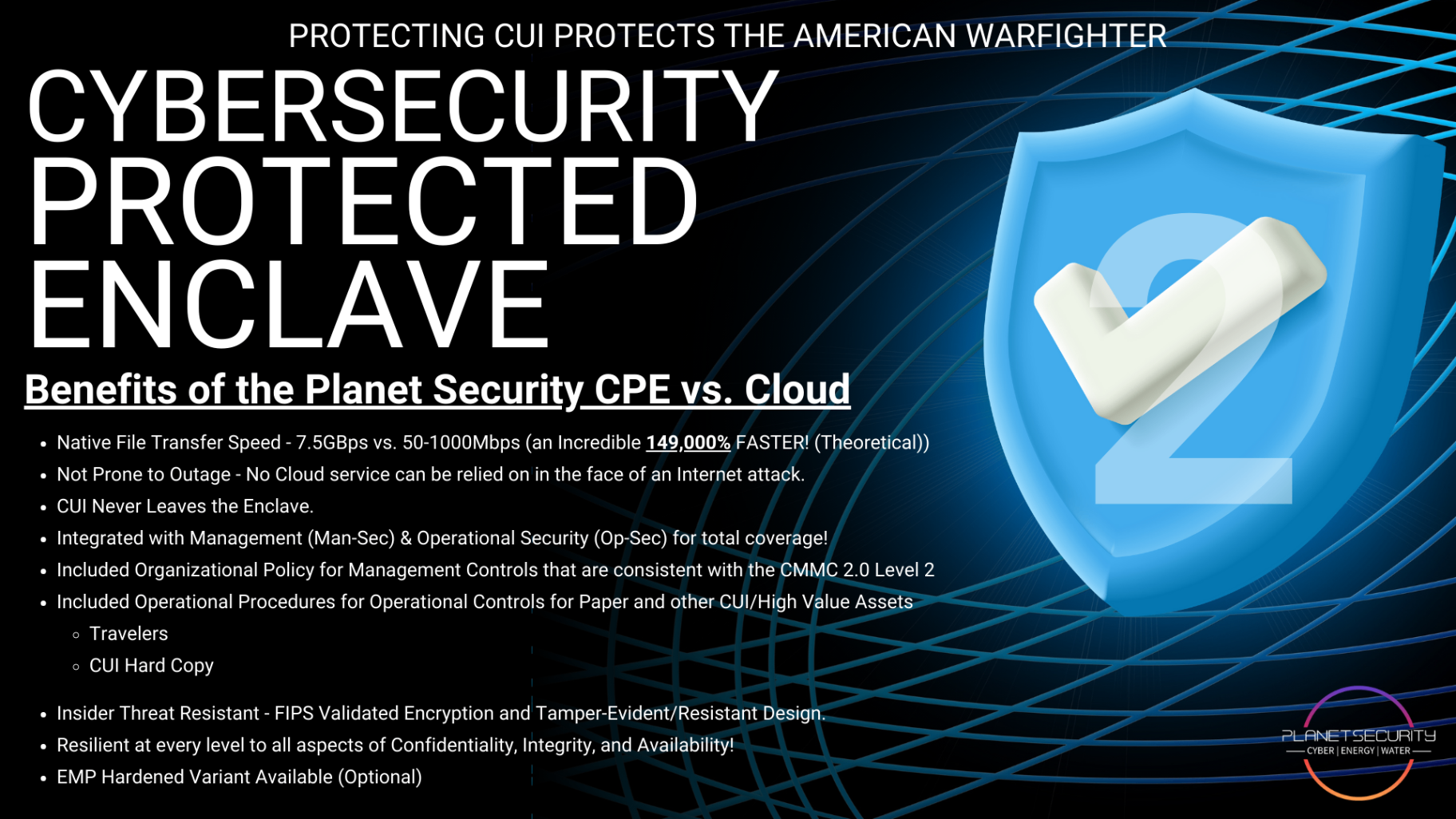
CPE Level 2 takes a completely different approach. Instead of trying to retrofit compliance onto your existing mess, it creates a dedicated, hardware-based protected enclave specifically designed for CUI.
Think of it this way: instead of trying to turn your house into Fort Knox, you build a proper vault next to your house. Your business keeps running exactly as it always has, while your CUI gets the military-grade protection it actually needs.
Built on the NIST Compliant Infrastructure Server
CPE Level 2 isn't some cobbled-together software solution. It's built on a purpose-designed NIST Compliant Infrastructure Server that meets every requirement for CMMC 2.0 compliance out of the box.
This means:
- No guesswork about whether your configuration meets standards
- No complex integrations between incompatible systems
- No surprise audit failures because something didn't work as expected
Turnkey and Affordable
Here's where CPE Level 2 gets really interesting. Because it's a complete, pre-configured solution, implementation takes weeks instead of months. You're not spending months figuring out how to make 20 different software packages work together: you're deploying a proven system that's ready to go.
The cost savings are massive:
- No expensive consultants trying to untangle your configuration mess
- No ongoing integration headaches that eat up IT resources
- No audit failures that cost you contract opportunities

Designed for CMMC 2.0 Levels 1 and 2 Compliance
CPE Level 2 covers every single requirement for CMMC 2.0 Level 2 compliance. We're talking about complete coverage of all 110 requirements and 320 assessment objectives. Not partial coverage. Not "most of the requirements." Every single one.
This comprehensive approach means:
- 100% audit readiness in approximately 4 weeks
- No Plan of Action & Milestones (POA&M) tracking required
- Complete protection for all CUI within the enclave
The Separation Advantage
The biggest advantage of CPE Level 2 is separation. Your CUI lives in its own dedicated environment, completely isolated from your business network. This separation solves problems that the all-in-one approach can't even address.
Business Operations Continue Unchanged
Your employees keep using the same systems they've always used for day-to-day business operations. Email, accounting, project management: everything stays exactly the same. Only CUI-related work moves into the protected enclave.
This means no productivity disruption, no retraining headaches, and no employee resistance to new systems they don't understand.
Clean Audit Trail
Auditors love clean separations. When CUI is handled in a dedicated environment with its own security controls, documenting compliance becomes straightforward. There's no confusion about which systems handle what data or which security controls apply where.
Reduced Attack Surface
Every system connected to your network is a potential attack vector. The all-in-one approach maximizes your attack surface by connecting compliance systems to business systems to external networks. CPE Level 2 minimizes attack surface by creating a separate, hardened environment for your most sensitive data.
Real-World Results
Let's talk about what actually happens when defense suppliers choose CPE Level 2 over the all-in-one myth:
- Audit-ready in 4 weeks instead of 12+ months of configuration struggles
- DODAM/DOWAM SPRS score of 110 with complete documentation
- No ongoing compliance headaches because the system just works
- Immediate cost savings from eliminated consulting and integration fees
The difference is night and day. Instead of spending a year trying to make incompatible systems work together, you get a proven solution that handles everything from day one.
The Bottom Line
The all-in-one myth persists because it sounds easy. But easy and effective are two very different things. When contract opportunities depend on CMMC compliance, you can't afford to bet on a approach that's designed to fail.
CPE Level 2 represents a fundamental shift from trying to force compliance onto existing systems to building compliance into the architecture from the ground up.
For defense suppliers who are serious about CMMC compliance: and serious about winning contracts: there's simply no substitute for a dedicated protected enclave. The all-in-one approach might sound appealing, but CPE Level 2 is what actually works.
Ready to move beyond the myth? Your CUI deserves better than a software band-aid on an business network. It deserves a real protected enclave built specifically for the job.
Phone: (702) 634-7233